Strong foundations for websites.
We design and operate modern infrastructure that keeps your website fast, secure, and continuously monitored. Our architecture reduces operational risk while minimizing long-term maintenance burden.
Reliability & Uptime
Proactive Maintenance
Automated uptime checks run every 60 seconds, with alerts triggered when performance or availability changes. Deployments include safeguards and rollback support to minimize disruption.
- 60-second uptime checks + alerts
- Release safeguards and rollback support
Real-Time Monitoring
Continuous signals help us detect anomalies early and respond quickly. Alerts and activity logs ensure transparency and documented oversight.
- Uptime and latency tracking
- Logged incidents and structured reporting
The Vector Gate
Every deployment passes through structured quality controls before release. Accessibility, security, and performance checks are verified prior to production.
Accessibility Validation
BUILDS INCLUSION
Automated checks verify alignment with accessibility standards and help reduce avoidable barriers.
Dependency Scan
THREAT DETECTION
Third-party packages are scanned for known vulnerabilities before release to reduce avoidable risk exposure.
Performance Gate
PROTECTS PERFORMANCE
Lighthouse and Core Web Vitals checks confirm performance targets are met before deployment.
Final Approval
RELEASE READY
A final review confirms deployment readiness before changes are released to production.
Designed for Security
Protection is embedded in the platform architecture, not layered on afterward.
WAF Protection
Edge-level web application firewall controls help mitigate common attack vectors such as SQL injection and cross-site scripting, with DDoS mitigation included.
SSL & Encryption
Encryption in transit is standard across managed sites. SSL certificates are automatically renewed and HTTPS is enforced with HSTS across all domains.
Dependency Monitoring
Third-party packages are continuously monitored for known vulnerabilities. Critical findings are prioritized and addressed when patches become available.
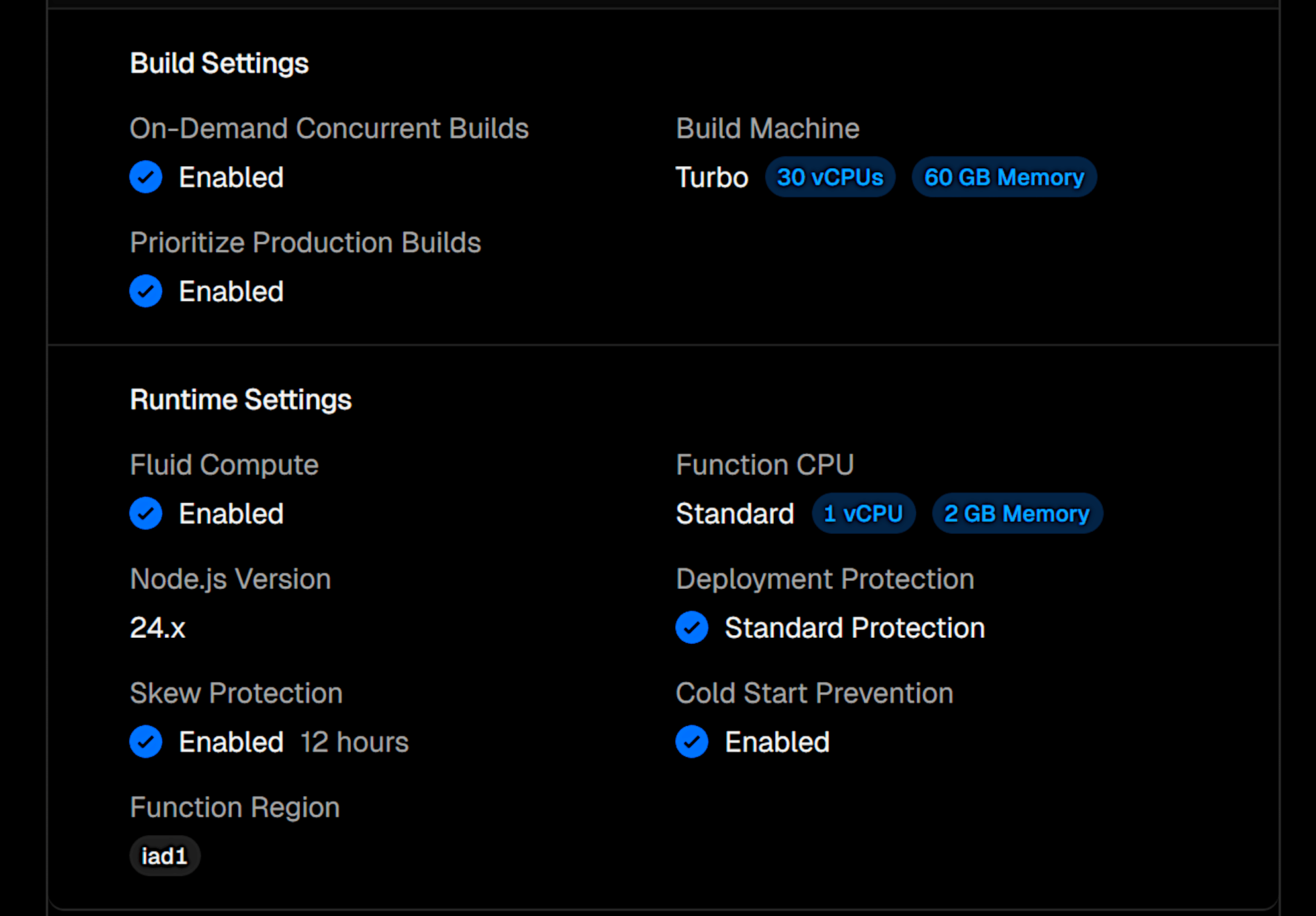
Visualizing the flow from the Edge Network and security layer through the deployment pipeline and into continuous monitoring.
System Reference Architecture
- Understand what is verified before launch and what is monitored continuously in production.
Powered by proven technology
Request an Architecture Review
We'll review your current infrastructure, identify potential risks, and outline a structured plan to improve performance, security, and operational reliability.